Coinbase has refuted the WSJ claims in a blog post, accusing the paper of confusing "client-driven activities" with prop trading. In a statement to the WSJ, published in the article alongside the allegations, a Coinbase spokesperson said that "Coinbase does not, and has never, had a proprietary trading business. Any insinuation that we misled Congress is a willful misrepresentation of the facts".
Wall Street Journal suggests that Coinbase tested proprietary trading
- "Coinbase Tested Group to Speculate on Crypto", The Wall Street Journal
- "In response to the Wall Street Journal", Coinbase
Investors seek to recoup around $30 million from Canadian "Crypto King" in his early 20s
So far, the court has seized two McLarens, two BMWs, and a Lamborghini — only a few cars out of the eleven luxury cars Pleterski owned, plus another four he was renting. Investors have also asked about the CA$45,000-a-month (~US$30,000) lakefront mansion he was renting in Ontario, watches, and gold bars, hoping they could be liquidated to repay some of his debts.
Pleterski had promised investors that he would invest on their behalf, taking 30% of any capital gains, with a goal of achieving 10–20% gains biweekly. He also promised that any loss on the initial investment would be paid back in full. Pleterski had made some money in crypto as a teenager, but according to him, he lost most of the money he was given to invest in late 2021 and early 2022 "in a series of margin calls and bad trades". An investor claims that at one point, he was given pictures and videos of financial statements showing an account with $311 million, but when he checked with the company supposedly maintaining the account, they said they had no accounts with that kind of funds. So far, the court and investors alike have struggled to untangle Pleterski's mess — according to him, he was unorganized and didn't track his finances or debts.
Wintermute hacked for $160 million
Wintermute hasn't disclosed more about the attack, but it's possible that the hacker may have exploited the vulnerability in the vanity wallet address generator Profanity, which was disclosed five days prior. The crypto asset vault admin had a wallet address prefixed with 0x0000000, a vanity address that would have been susceptible to attack if it was created using the Profanity tool.
This is the second incident involving Wintermute in the past few months. In June, the group provided the wrong wallet address to the Optimism project, and Optimism sent 20 million OP tokens to a non-existent address. Another person noticed the error before they did and was able to take the tokens. They ultimately returned 17 million of the tokens to Wintermute, keeping the rest as a "bounty". $OP have been trading at around $1 as of mid-September.
SEC files emergency action to stop CryptoFX scam
The United States Securities and Exchange Commission filed an emergency action to stop the fraud and freeze assets, which was granted on September 29, 2022. The SEC then filed a complaint against the company and its leaders Mauricio Chavez and Giorgio "Gio" Benvenuto. The SEC alleged CryptoFX had raised at least $12 million from 5,000 investors, which ostensibly would be put into crypto markets but instead was primarily used to "fund [Chavez's] real estate company and extravagant lifestyle".
- "SEC Halts Crypto Asset-Related Fraud Victimizing Latino Investors", United States Securities and Exchange Commission
Sparkster settles for $35 million with the SEC; SEC charges crypto influencer
The SEC also charged crypto influencer Ian Balina for his involvement with the scheme. He allegedly accepted a 30% bonus on the $5 million worth of SPRK tokens he purchased in an agreement to promote the project on YouTube, Telegram, and other channels, but did not disclose his compensation. He also organized an investing pool with more than 50 investors, and also didn't register it with the SEC. Balina had advertised that he could help people "make millions with initial coin offerings".
- "Sparkster to Pay $35 Million to Harmed Investor Fund for Unregistered Crypto Asset Offering", U.S. Securities and Exchange Commission
- U.S. SEC v. Ian Balina
UK financial regulator warns against FTX exchange
A spokesperson from FTX said they believed that "a scammer is impersonating FTX", which they said they thought led to the warning. However, that statements in the warning are accurate: FTX is not registered with the FCA, and they serve UK customers.
- FTX, Financial Conduct Authority
- "UK Regulator Issues Warning on Crypto’s FTX to Consumers", Bloomberg
Scammer earns 13 ETH ($17,500) from fake Mutant Ape scheme
The trader ended up with a worthless counterfeit and a measly 0.5 ETH for his pricey NFT. The scammer quickly flipped the real Mutant for 13.5 ETH, making a tidy $17,500 profit.
Whale illustrates price manipulation risk in GMX exchange, profits more than $400,000
A whale was able to take advantage of this "feature" by taking large positions in AVAX, the token belonging to the Avalanche blockchain, which has relatively low liquidity compared to larger tokens like Bitcoin or Ether. The whale then manipulated the price by making large trades on a centralized exchange, taking an estimated profit of between $400,000 and $450,000 after fees.
Some had publicly expressed concerns about the possibility of such an exploit earlier in September: Taureau, a founder of another decentralized exchange, had outlined the possibility of an exploit like this on a podcast episode on September 1.
GMX responded to the incident by capping the size of positions that users can take on AVAX. Another project, MM.Finance, announced they would be pausing order execution on their MadMex platform, which is a fork of GMX.
Binance accounting bug involving Helium tokens results in $19 million of erroneous payouts
Binance distributed around 4.8 million HNT before discovering and patching the bug, valued at around $19 million.
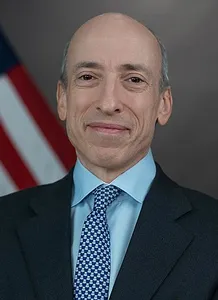
Hours after Ethereum transition to proof-of-stake, SEC Chair says PoS crypto could be classed as securities
Later that day, SEC Chairman Gary Gensler pointed to the staking mechanism as a signal that an asset might be a security as determined by the Howey test.
There has been much discussion over whether cryptocurrencies in general or individually should be considered securities, commodities, or possibly even something else. Broadly, people within the crypto community don't want to see the assets fall under SEC jurisdiction, as the SEC is seen as much less friendly to the industry than the CFTC.
- "Ether’s New ‘Staking’ Model Could Draw SEC Attention", The Wall Street Journal