Victims estimate that between €1.5 million and €4.5 million (~$1.54 million – $4.64 million) was stolen.
Hengelo man arrested in alleged crypto pyramid scheme
Man reports losing $100,000 to website spoofing a crypto exchange
The man contacted Canadian police, who told him the assets had been transferred out of the country and that they were unable to trace it.
NoOnes hacked for almost $8 million
Youssef emphasized that user funds were safe, which led to questioning from others on how that could be possible when nearly $8 million had been stolen. Youssef claimed he had reimbursed the stolen assets himself.
- Telegram post by zachxbt [archive]
- Tweet by Ray Youssef [archive]
Feed Every Gorilla hacked again for over $1 million
This time, the FEG project team blamed an issue with the project's bridge, which is a tool used to deposit and withdraw tokens from the project. An attacker was able to maliciously withdraw a large amount of FEG tokens via the flaw in the bridge, which they then sold off for around $1.07 million, tanking the FEG token price by 99% in the process. The bridge had been audited by the PeckShield blockchain security firm.
SEC fines Jump Crypto subsidiary $123 million
The SEC also found that Tai Mo Shan had acted as a statuary underwriter for the Terra sister token Luna, which was an unregistered security.
Tai Mo Shan agreed to the fine, and to a prohibition on future violations of securities laws.
- “Tai Mo Shan to Pay $123 Million for Negligently Misleading Investors About Stability of Terra USD”, U.S. Securities and Exchange Commission [archive]
Two NFT fraudsters charged for rug pulls amounting to over $22 million
For example, a "Vault of Gems" NFT project falsely claimed to be the "first NFT pegged to a hard asset, like jewelry", which would have its own exchange. A "Faceless" NFT project promised to produce comic books, a movie, and a clothing company. None of the promises ever materialized, and Hay and Mayo abandoned the projects soon after launching them.
Hay and Mayo worked to hide their involvement with their scams, and have been charged with harassment for attempting to threaten those who connected them. In one case, after a person revealed Hay and Mayo to be the ones behind the Faceless NFT project, the duo sent threatening emails and text messages to the man and his parents. In an email to his parents, they impersonated a law firm, and even threatened to make false sexual abuse claims against the man.
- Indictment of Gabriel Hay and Gavin Mayo [archive]
Kraken fined $5.1 million by Australian securities regulator
The more than 1,100 customers lost more than US$5 million. While some of the customers were likely sophisticated investors, Kraken made no effort to limit the product to such a group. Around 81% of the customers who used Kraken's margin product lost money.
This is far from Kraken's first run-in with regulators. The company has settled with US regulators over sanctions violations and failure to comply with securities regulations pertaining to its staking product. They also have an open lawsuit from the US SEC over alleged unregistered securities offerings and commingling corporate and customer funds.
- "Kraken crypto exchange operator to pay $8 million following ASIC enforcement action", Australian Securities and Investments Commission press release
Crypto holder loses assets priced at $2.5 million
Some blamed the theft on an apparent malicious Ethereum transaction the user had signed nearly three years prior. However, while a malicious transaction signature on Ethereum could explain the NFT thefts, it should not alone enable the theft of assets on the separate bitcoin blockchain.
Despite this, Ledger blamed its customer, telling a media outlet that "As we know, the user got phished when it comes to the ETH wallet, we can assume user error on the BTC side too".
Former pastor charged with crypto scheme in which he stole $5.9 million from his former congregants
Despite his promises, Pinillo had created no trading platform whatsoever, was doing no crypto trading, and simply pocketed all the money. Any payments made to his customers during the fraud were taken from newer investors, in classic Ponzi fashion.
- "CFTC Charges Washington State Pastor with Fraud, Misappropriation in Multilevel Marketing Scheme Targeting Hispanic Americans", US Commodity Futures Trading Commission [archive]
Clober gets clobbered
Clober has offered a 20% "bug bounty" to the exploiter vi on-chain message, though they have not yet received any public reply.
- "Clober Dex Incident Analysis", CertiK
Alpaca Finance proposes $50,000 restitution for $2.8 million in losses
Then, when a new token called THENA was listed on Binance and experienced major volatility as trading opened, Alpaca's issues came to a head. As the token price surged, the slow oracle failed to reflect price changes, allowing people to withdraw far more THENA than they had posted as collateral. THENA lenders have lost an estimated $2.8 million.
On December 10, Alpaca Finance proposed distributing $50,000 "saved" by their liquidation bot to the lenders who had lost funds. Alpaca Finance also banned users complaining about their losses in the project Discord, dismissing them as a "group bot/FUD attack".
85-year-old painter loses life savings to NFT art dealer scam
Police were unable to recover his money, although they did seize around 40 websites that were spoofing various real NFT marketplaces.
- "Brooklyn District Attorney Shuts Down 40 Domains Associated With NFT Crypto Scam Targeting Artists, After Brooklyn Painter Lost Over $135,00", "Kings County District Attorney's Office" [archive]
"Hawk tuah" memecoin immediately crashes
The token followed the typical pattern of quickly pumping, then crashing spectacularly, losing around 90% of its "value". This is often an indicator of a pump-and-dump scheme by insiders, but Welch vehemently denied such wrongdoing, blaming the crash on "snipers".
"I really lost $43k apeing in 'hawk tuah' coin," wrote one buyer on Twitter. Other Twitter users marveled at a wallet that swapped $1.4 million worth of MOODENG (a memecoin based on the tiny hippo of the same name) only to lose it all on the $HAWK token.
Nike to shut down its RTFKT "virtual sneakers" project
However, the "metaverse" trend failed to take off, and Nike is only the latest company to abandon its multi-million dollar investment in the space.
Official Solana JavaScript library compromised in supply chain attack, at least $184,000 taken
Malicious versions of the library allowed exploiters to steal private keys and drain funds from dApps like various Solana bots.
Around $184,000 was stolen as a result of the compromise. Although it was caught fairly quickly, and the malicious code was removed from package managers, developers will need to update projects that used the malicious version of the library, and refresh any potentially exposed secrets.
- "Solana Web3.js library backdoored to steal secret, private keys", Bleeping Computer [archive]
Clipper DEX suffers $450,000 hack
Although the $450,000 theft is relatively small compared to some other crypto hacks, it represented around 6% of the total value locked on Clipper. Clipper stated they were working to trace and attempt to recover funds, and asked the hacker to contact them to potentially negotiate a return of some funds.
Crypto exchange XT.com suffers $1.7 million hack
13-year-old rug pulls crypto token, then faces retaliation
Around $21 million in losses reported by users of DEXX
DEXX did not disclose how much was taken in the breach, but hundreds of victims have reported around $21 million in combined losses so far.
Polter Finance exploited for $12 million
The creator of the platform stated that they had filed a police report with Singaporean authorities. They also attempted to contact the hacker via on-chain message to negotiate the return of funds, but have not received a response.
Thala Labs loses, then recovers, $25.5 million
DeltaPrime loses $4.8 million in second hack
DeltaPrime paused the protocol on both Arbitrum and Avalanche, stopping the attacker from being able to steal more funds than they already had.
DeltaPrime was hacked previously on September 16, losing $6 million after a leaked private key enabled an attacker to mint a huge number of the platform's stablecoin deposit receipts.
Trader reveals he lost $28 million to bad copy-paste
Short of finding a vulnerability in Renzo, the trader's only real choice is to plead with Renzo to change their smart contract in such a way as to release the funds. While this is technically possible, Renzo has told the trader they could not grant his request due to "regulatory limitations".
CoinPoker exploited for $2 million
The platform sent a message to the exploiter attempting to negotiate a return of some of the funds.
MetaWin casino hacked for $4 million
- "Online Casino MetaWin hacked for $4 million — ZackXBT", CoinTelegraph
Supply chain attack stemming from JavaScript animation library results in losses for users of 1inch and other platforms
Other crypto platforms affected included TEN Finance and Movement. Because the animations library is widely used, other non-crypto-related websites also showed the prompt.
M2 cryptocurrency exchange hacked for $13.7 million
Shortly after the theft, M2 acknowledged the hack and announced that "the situation has been fully resolved". This apparently involved M2 restoring customer funds from their own assets, rather than recovering the stolen assets.
Sunray Finance hacked for $2.7 million
In the process of selling off tokens, an arbitrage bot was able to take advantage of the price difference by selling the rapidly crashing SUN token into a second liquidity pool that apparently went unnoticed by the hacker, and the bot operator also profited around $560,000.
$20 million moved from US government wallet in possible theft
The government has not made any statements regarding the movement of assets.
The following day, $19.3 million in tokens were returned to the original wallet.
Sharpei memecoin rug pulls for $3.4 million
As the token price stuttered along with these revelations, insiders apparently decided to quit while they were ahead, and cashed out in a quick and coordinated sale.
Blockchain company Forte acquires games studios, demands secrecy, shuts them down
Both studios had several games in progress, and two of Phoenix Labs' games were explicitly designed for younger players. Developers reportedly voiced discomfort with incorporating blockchains into the games, selling digital items to children.
Later, Forte pulled the plug on several in-development games at both studios. Then, Forte shut down Rumble in 2024, laying off all employees. Forte also laid off over 100 people from Phoenix Labs that year.
Tapioca DAO exploited for most of its assets — over $4 million
Various security researchers have observed that the attack appears to be linked to a slew of social engineering attacks perpetrated by cybercriminals out of North Korea.
Radiant Capital exploited again, this time for at least $50 million
This is the second Radiant Capital exploit this year, after a $4.5 million theft in January that was enabled by an unaddressed vulnerability in the underlying Compound Finance code.
The US and South Korean governments later attributed this attack on Radiant to North Korean state-sponsored attackers.
Cosmos founder reveals a portion of the protocol was created by North Korean developers
Kwon urged the Cosmos governance team to perform a full audit of the code written by these developers, and develop more protocols to prevent issues like this going forward. He also called for the governance team to blacklist Zaki Manian.
- "On the LSM Module", All In Bits
Permit phisher steals almost $1.4 million in frog tokens
The attacker stole around $1.1 million of the cartoon frog-themed PEPE tokens, and another roughly $50,000 of the also cartoon frog-themed APU token.
$3.1 million in EIGEN tokens stolen and sold
After the incident, some questioned why the tokens had been sent to an investor without a vesting contract, given they were supposed to be locked for a period of time to prevent sale.
Victim loses over $32 million to wallet drainer
The victim wallet sent a message to the thief, offering "a peaceful resolution to this situation" in which the thief could keep 20% of the total amount taken (around $6.5 million).
Bedrock staking platform loses $2 million after bug that allowed users to trade Bitcoin and Ethereum 1:1
A security firm working with Bedrock had tried to warn Bedrock of the vulnerability several hours before the attack, but the team was asleep. The vulnerable contracts had been deployed a day and a half prior to the attack, and had not been audited.
Fortunately for Bedrock, security groups were able to pause third-party projects surrounding Bedrock, which helped to limit the losses — which ultimately could have been as high as the entire value of funds on the protocol.
Onyx hacked for $3.8 million via the same exploit used against them less than a year ago
Onyx apparently didn't learn their lesson the first time around, when they were exploited for $2 million in November 2023 by an attacker taking advantage of a known vulnerability affecting empty markets on the protocol. This same bug seems to have contributed to this exploit, although Onyx has claimed the hack was due to a separate vulnerability in an NFT liquidation contract.
Truflation hacked for around $5 million
Truflation is a blockchain-based project that provides economic data including inflation rates and asset valuations. The platform has been backed by Coinbase Ventures, Chainlink, and others.
OpenAI Twitter account once again hacked and used to promote scam token
This latest hack is only the latest in a slew of Twitter account compromises "announcing" a scam token. Over a year, OpenAI CTO Mira Murati had her account hacked to promote an "$OPENAI" token. Three months ago, accounts belonging to chief scientist Jakub Pachocki and researcher Jason Wei were hacked and used to post the same scam as today.
Shezmu hacked for almost $5 million, negotiates bounty
Shortly after the attack, Shezmu offered a 10% "bounty" for the return of the funds. The attacker responded that they would only consider a 20% bounty. Shezmu agreed to the terms, and announced to their followers that they had achieved a recovery from the "white hat" hacker.
BingX hacked for $52 million
Some accused the exchange of trying to cover up the theft by announcing "temporary wallet maintenance" without disclosing that a theft had occurred. The team later announced that "there has been minor asset loss", and stated that the lost funds would be restored out of the company's capital.
Around $10 million of the stolen assets were frozen during recovery efforts after the theft.
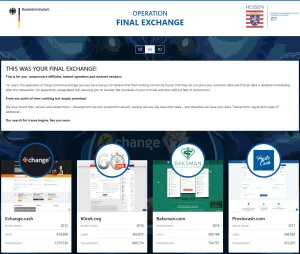
Germany seizes 47 cryptocurrency exchanges reportedly used by ransomware groups
Websites for these exchanges now show notices announcing a law enforcement operation called "Operation Final Exchange". The page announces to visitors "This was your final exchange!", and in a letter addressed to "ransomware affiliates, botnet operators and darknet vendors", warns that authorities are now working to trace the illicit users of the exchange.
- "Germany seizes 47 crypto exchanges used by ransomware gangs", BleepingComputer
Almost $2 million taken from users of Telegram "Banana Gun" crypto trading bot
Banana Gun acknowledged the attack on Twitter and shut down the bot. They posted that they did not believe their backend was compromised, and stated that they believed the attack occurred via a "front-end vulnerability" — though it was not clear what this might have referred to.
- "Telegram bot Banana Gun’s users drained of over $1.9M", CoinTelegraph [archive]
Arrests made after $243 million stolen from one individual in Gemini phishing attack
The FBI raided a luxury home in Miami in connection to the theft, and arrested two men in their early twenties. Authorities worked with crypto investigators including zachxbt to trace the stolen funds.
Rari Capital settles with the SEC
The company and co-founders will pay fines, and the individuals will agree to five-year bans from serving as officers or directors.
The regional SEC director stated, "We will not be deterred by someone labeling a product as 'decentralized' and 'autonomous'," alluding to crypto firms' tendencies to try to skirt securities regulations by claiming to be "decentralized".
Rari has featured on Web3 is Going Just Great before, when they were exploited for around $80 million in April 2022 and when they were exploited for around $15 million in May 2021. The project effectively wound down soon after the second theft.
- "SEC Charges DeFi Platform Rari Capital and its Founders With Misleading Investors and Acting as Unregistered Brokers", U.S. Securities and Exchange Commission [archive]
Ethena website compromised
They later were able to deactivate the website and regain control of the domain. "Remember scammers are always chasing you," they wrote on Twitter.
$6 million taken from Delta Prime defi protocol
DeltaPrime acknowledged the attack on Twitter, and announced that "the risk is contained". They also stated that they were "looking into other ways to reduce user losses to a minimum", including by pulling from the protocol's insurance pool.
Flappy Bird creator disavows crypto spin-off
Nguyen famously removed the game from app stores shortly after it surged to popularity, stating that he felt guilty that people were becoming addicted to the game. This makes the game's reappearance — complete with loot boxes and other addictive features — feel somewhat dark.
On September 15, Nguyen returned from a seven-year Twitter hiatus to post: "No, I have no related with their game. I did not sell anything. I also don't support crypto."
Although Nguyen held the Flappy Bird trademark, he did not sell it to this group. Instead, they registered the trademark themselves after arguing he had abandoned it.